Mail Access Combo Txt: Download 192k
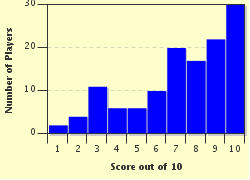
This is my first quiz good luck! Spoiler Alert. You have been warned
- Home
- »
- Quizzes
- »
- For Children Trivia
- »
- Riordan, Rick
- »
- Download 192k Mail Access Combo txt
Services like "Have I Been Pwned" allow users and administrators to check if their credentials have appeared in public combo lists and data breaches.
The data found in combo lists is rarely generated from scratch. Instead, it is typically compiled from historical data breaches across various websites and services. When a platform suffers a data leak, malicious actors often aggregate the exposed credentials into massive collections to distribute or sell on the dark web and specialized forums. Download 192k Mail Access Combo txt
In conclusion, a "192k Mail Access Combo txt" file is a stark reminder of the ongoing challenges in digital security. It represents the residue of past data failures and the raw material for automated cyberattacks. By understanding what these files are and how they are used, the cybersecurity community can better anticipate threats and enforce the defensive measures necessary to protect global digital infrastructure. Services like "Have I Been Pwned" allow users
MFA ensures that even if a password from a combo list is correct, the attacker cannot gain access without a second verification step. When a platform suffers a data leak, malicious
The existence of a "192k" list highlights a major vulnerability in user behavior: password reuse. Because many individuals use the exact same password across multiple platforms, a leak on a single low-security website can compromise their highly sensitive accounts, including personal or corporate email. Email access is particularly dangerous because it often serves as the master key for resetting passwords on banking, social media, and cloud storage accounts. Defensive Measures and Ethical Considerations